Two Factor Authentication – A Huge Risk & Insecure
- I bought an Apple Ipad Pro at the Apple Store and I logged in with my apple id at the store.
- I did not have my other registered device, which was an iphone, with me while I was travelling in USA.
- It asked me for a verification code sent to my other device, but since I did not have access to it, I could not enter it.
- A couple of minutes later I got an email from Apple saying that my registered other device phone number has been changed.
- A few minutes later I got another email that my date of birth has been changed.
- I tried logging in through the web, but it would ask me for the verification code or the new other device phone number. But since this had changed, there was no way it would let me go through.
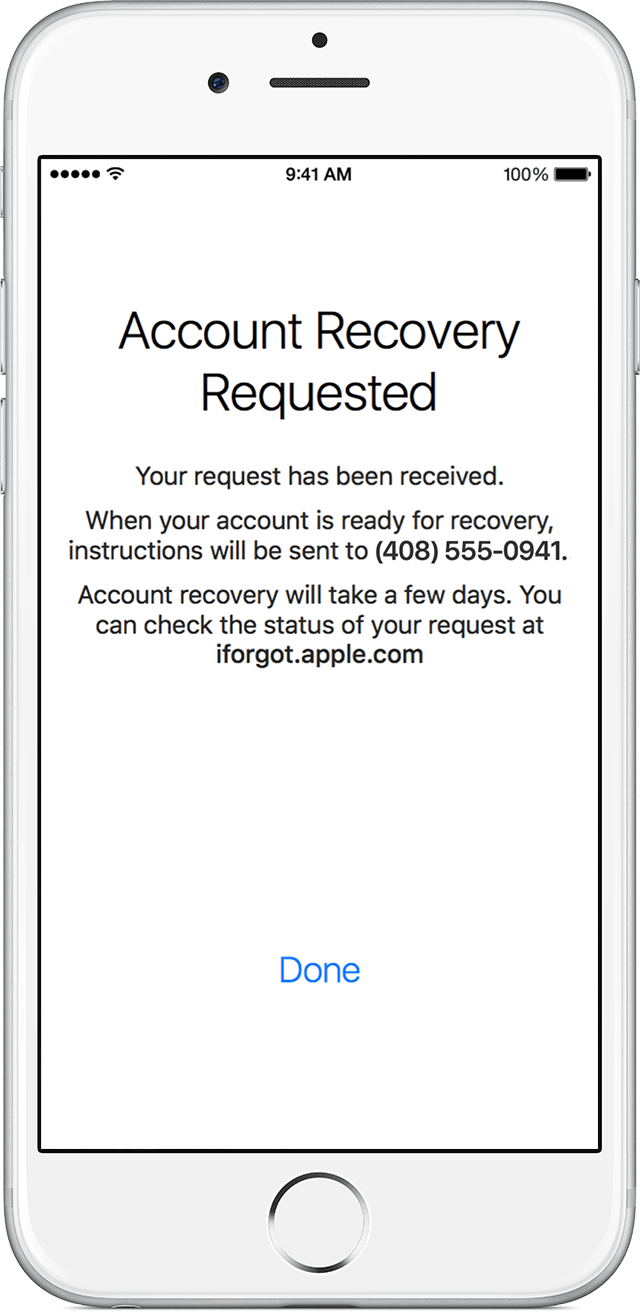
I logged a case with Apple support but they claimed that they were unable to help and I would need to provide the changed phone number or else they could not verify my identity.
On coming back to India I see another device added to Find My Phone under the name Ayaan ****. I am worried because this hacker would now be accessing all my phone data, my icloud data and could also be using my credit card associated with the apple id. I logged another case with Apple support when I came back to India a few days later and again they could not do anything in the absence of the new phone number. I put an Erase on this other device of Ayaan **** through find my phone app. Apple would not help at all.
When I try logging in with my apple id, it lets me go through the 1st step if I use my original password and then it ask me the verification code. If I put an incorrect password it would not let me proceed saying incorrect password.
I still have access to the email associated with the apple id and the credit card details associated with the apple ID are still mine. I argued that a my email and my credit card would be a more secure way for verifying my id because they are more secure than a phone device. Apple insist that the only way they can verify my identity is if I give them the other device phone number. It is crazy that my id verification is restricted to a mere device that can be lost or stolen and accessed by almost anybody. And in case I happen to lose this, all my personal / business data and my finances are at the risk of being used by a hacker.
- It is very surprising that the hacking happened from an Apple Store, which would mean their network is compromised.
- The hacker changed the phone number – which means that the Two Factor Authentication is not as secure and has loop holes.
- Apple ID is solely dependent on the other device which is the least secure device as it can be stolen, lost or accessed by anybody when left alone for a few moments.
- Apple needs to add the email security also to its apple id authentication. Email are not mobile and would be more secure.
I have lost complete trust in the Apple Two Form Authentication and would appreciate any help to recover by apple id
<Personal Information Edited by Host>
iPad Pro, iOS 9.3.2, null