The hack that permits iCal notices that cannot be blocked is easily converted to an attack.
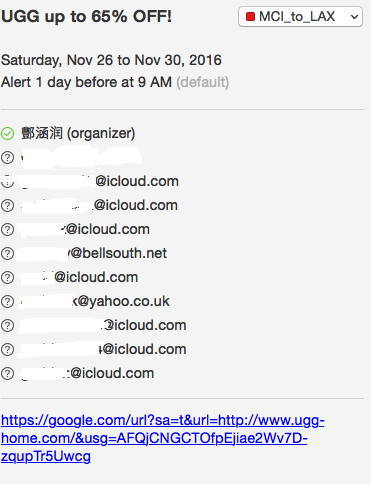
Consider how useful your OSX / iOS device will be if you start receiving notices at the rate of one, or one thousand, per second. If the hack permits access to old, random-named, calendars - as it did this past weekend with a special 2010 calendar of mine only used for a few months in one of my cases back then (screen capture below) how hard will it be for the hacker(s) to define a shared calendar using your ID and notify you from that calendar? I think that's what's happened to you where you don't have iCloud calendars enabled.
Weaponizing this hack is a certainty - the only question is when will it happen?
I've looked at iCal in Activity Monitor and it is deeply tied to OSX - and, given the lesser controls under iOS - iCal must have even deeper hooks in that OS.
Short of turning off all Internet access, there is no defense.
The only way that I know of to do anything constructive is by making Apple service requests about the bug in iCal by contacting support: https://support.apple.com/contact.
I've seen reports of this bug dating back several years. What I haven't seen in those years is the number of these SPAM reports that we are seeing today. When the New York Times publishes the iCal and Photo sharing bug in addition to 9 to 5 Mac and other Mac sites, this problem is growing.
The "fix" in iCloud to turn off in-app notifications had no effect on this last Notification - an Ugg phishing notification. Screen capture follows: note - not all email addresses are iCloud and neither are they limited to US email accounts.